Modern access operations for mobile keys, smart readers, and audit-ready rollout.
NG-Key brings mobile enrollment, passkeys, NFC credentials, cloud-connected readers, and verifiable audit visibility into one operating model for teams that need rollout control, reliable daily operations, and a clean path to expansion.
A visual layer for rollout, onboarding, and daily operations.
Use-case visuals help explain how NG-Key connects enrollment, credentials, reader operations, and audit visibility in one operational flow for customers, partners, and delivery teams.
Show mobile onboarding, passkeys, and credential rollout with clear visual context.
Present controllerless readers, direct connectivity, and operational readiness in one story.
Support go-live and procurement conversations with traceable operational narratives.

This visual supports the explanation of enrollment, operations, and audit visibility across the NG-Key platform.
AI that helps operations teams, customer stakeholders, and channel sales act faster.
NG-Key now turns platform signals into serious business guidance. The AI layer does not replace operational control. It summarizes rollout posture, highlights blockers, recommends the next action, and gives customer, admin, and partner teams a clearer basis for go-live, expansion, reference conversations, and scheduled stakeholder reporting.
Inside the tenant dashboard, the AI rollout copilot shows whether user activation, credential adoption, reader coverage, and support stability are strong enough for the next rollout phase.
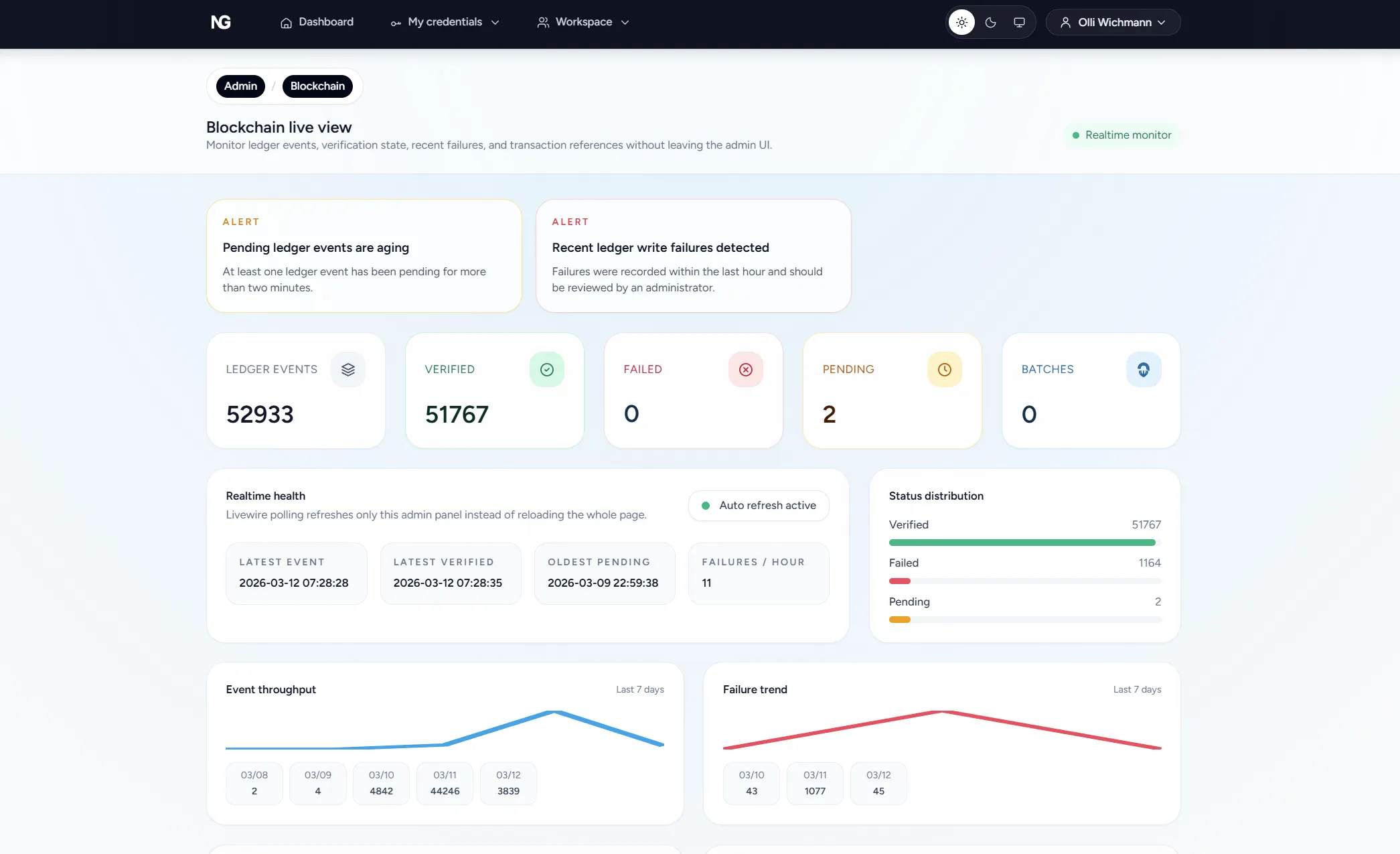
For platform operators, the monitoring AI highlights queue pressure, reader availability, latency, ledger health, and runtime anomalies with clear operational next steps, while the reporting layer packages the same posture into scheduled admin digests.
A dedicated reseller portal uses the same AI foundation for workspace blockers, commercial follow-up, project handover, and partner program execution.
A complete access platform instead of disconnected point tools.
The platform is structured around the operational components you actually need in the field: identities, Microsoft Entra ID capable sign-in flows, FIDO2 and WebAuthn credentials, NFC mobile keys, smart readers, credential-media assignments, permissions stored directly on the reader, direct cloud provisioning, schedules, admin reporting, audits, ledger events, and clear visibility into what happened when.
Guide users from invitation to enrolled phone with a controlled onboarding flow for NFC mobile keys.
Connect tenant workspaces to Microsoft Entra ID for Azure based sign-in and cleaner enterprise identity alignment.
Use public-key credentials with device-bound private keys and local user verification instead of relying on conventional static card identifiers.
Provision reader settings, claim flows, NFC mobile key approval logic, and live operational state directly without adding separate on-site controller infrastructure.
Apply access windows, area assignments, and repeatable access presets without spreadsheet drift.
Deliver personal daily, weekly, or monthly monitoring digests with incident aware summaries for platform admins.
Translate high-level grants into effective permissions stored directly on the reader so approval continues even when connectivity is interrupted.
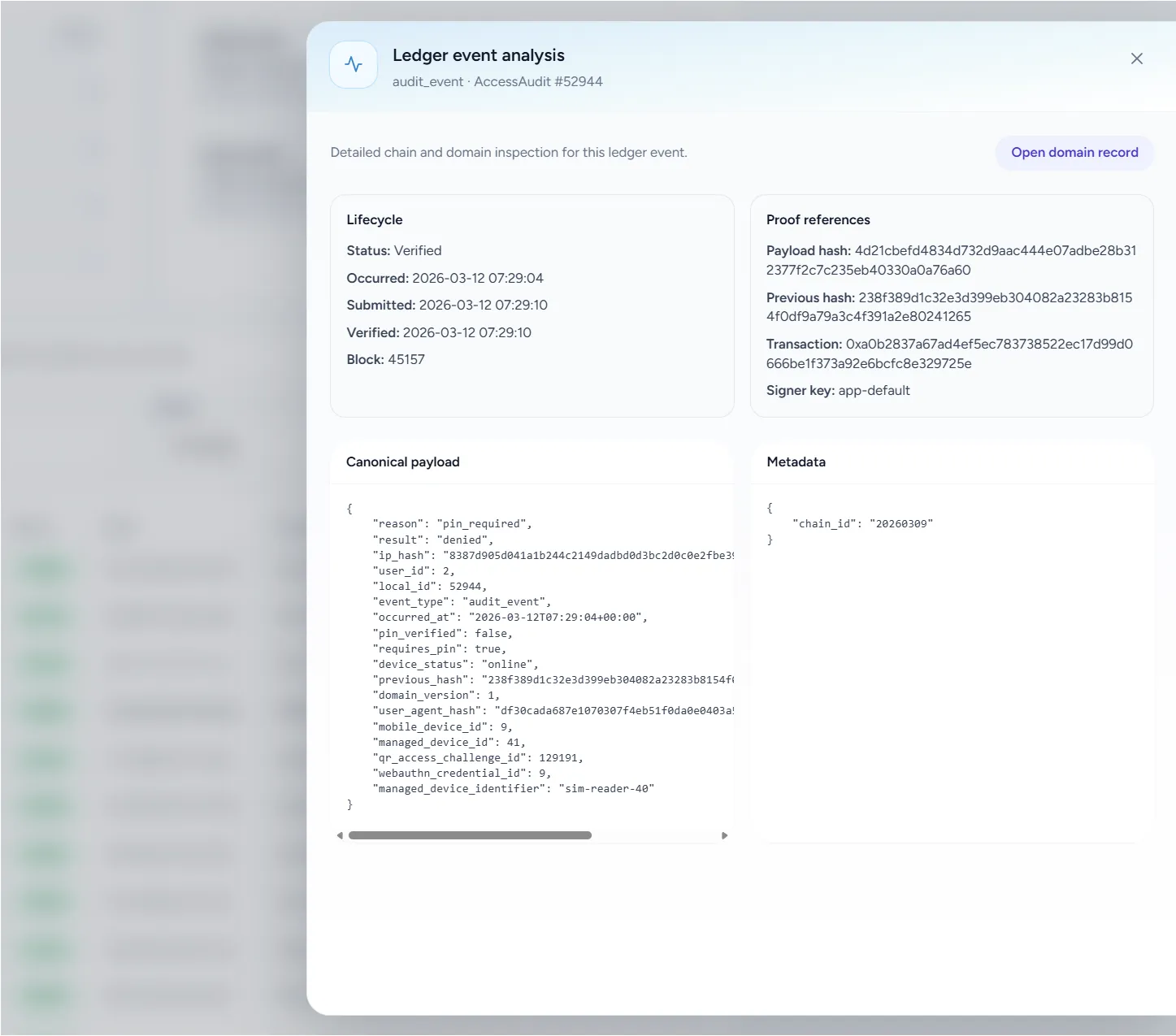
Track operational history, access decisions, ledger events, and blockchain-backed verification from the same system context.
A simpler operating model than classic controller-based access stacks.
The biggest difference is not only in the UI. It is in the architecture: permissions live on the reader, onboarding happens through a fast QR flow, NFC mobile keys can also be used directly at the reader, and cloud connectivity stays direct instead of passing through extra controller layers.
A clear operational flow from identity onboarding to reader decision traceability.
Create identities and prepare them for controlled enrollment.
Bind devices and public-key credentials to a defined user lifecycle.
Map users or groups to readers, areas, and schedule presets.
Scan the reader QR code, complete the claim flow, and bring the device online in under a minute.
At the reader the flow is NFC tap, local Face ID or biometric verification, signed token exchange, and door approval with central audit visibility.
The world's fastest smart reader enrollment.
Q-Air provisioning is instantaneous. Scan a QR code, the reader is online, configured, and access-ready — in under 60 seconds. No cables. No controllers. No commissioning overhead.
Scan the reader's unique QR code with the Q-Air app. The device is claimed, configured, and online — zero manual input required.
Permissions, schedules, and access policies are pushed to the reader in real-time over a direct MQTT connection — no on-site controller required.
From unboxing to access-ready: mount the reader, scan the Q-Air QR, and the door is live. The fastest reader enrollment in the industry.
 by NG-Key
by NG-Key
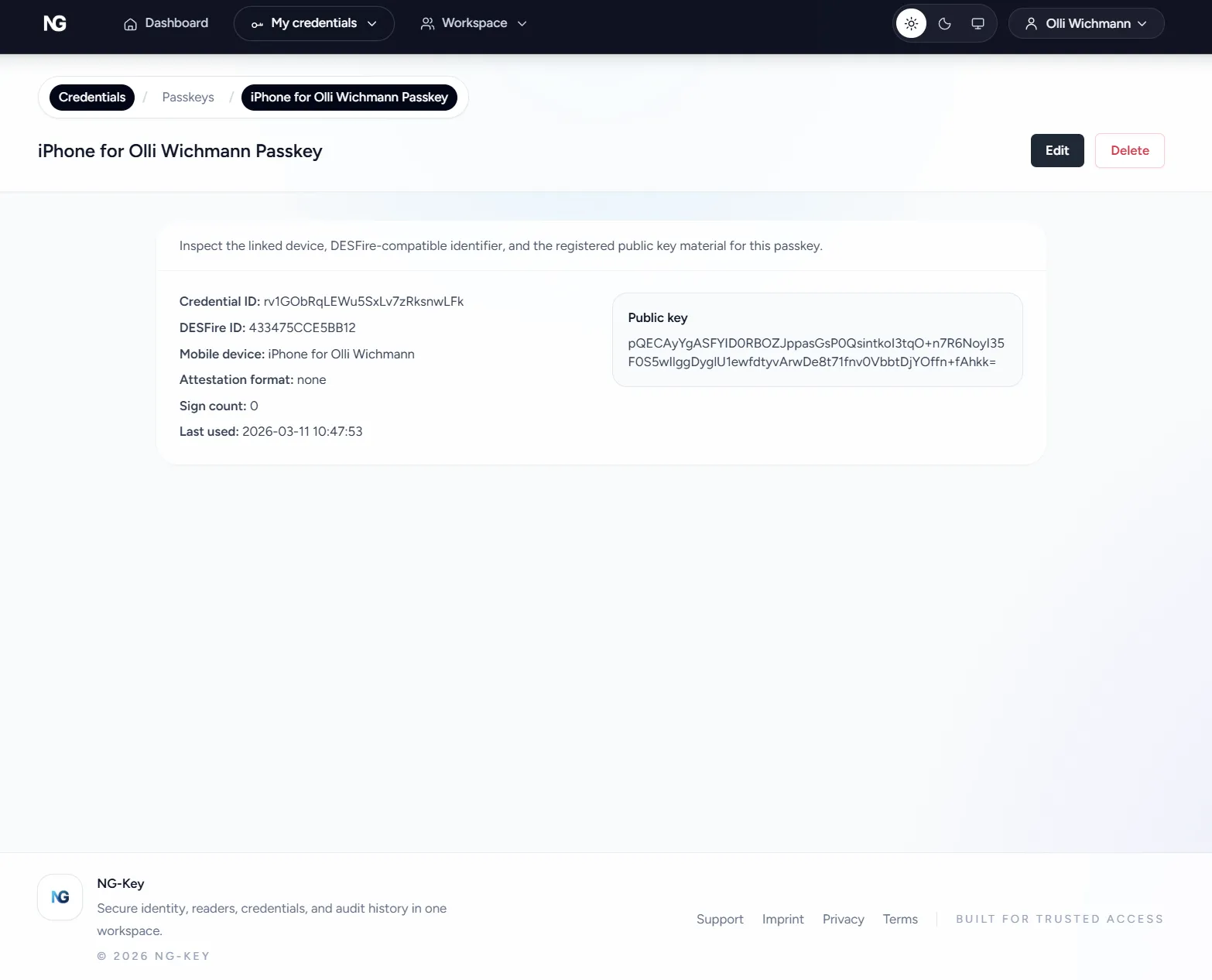
Credential operations stay tied to real devices, users, and enrollment state.
See which phones are active, enrolled, and connected to the identity lifecycle.
Track WebAuthn credential registration, public key state, transports, device association, and DESFire-linked identifiers where physical media is part of the rollout.
Use device-bound cryptographic credentials with local user verification, while still supporting controlled card or transponder assignment flows for deployments that use physical media.
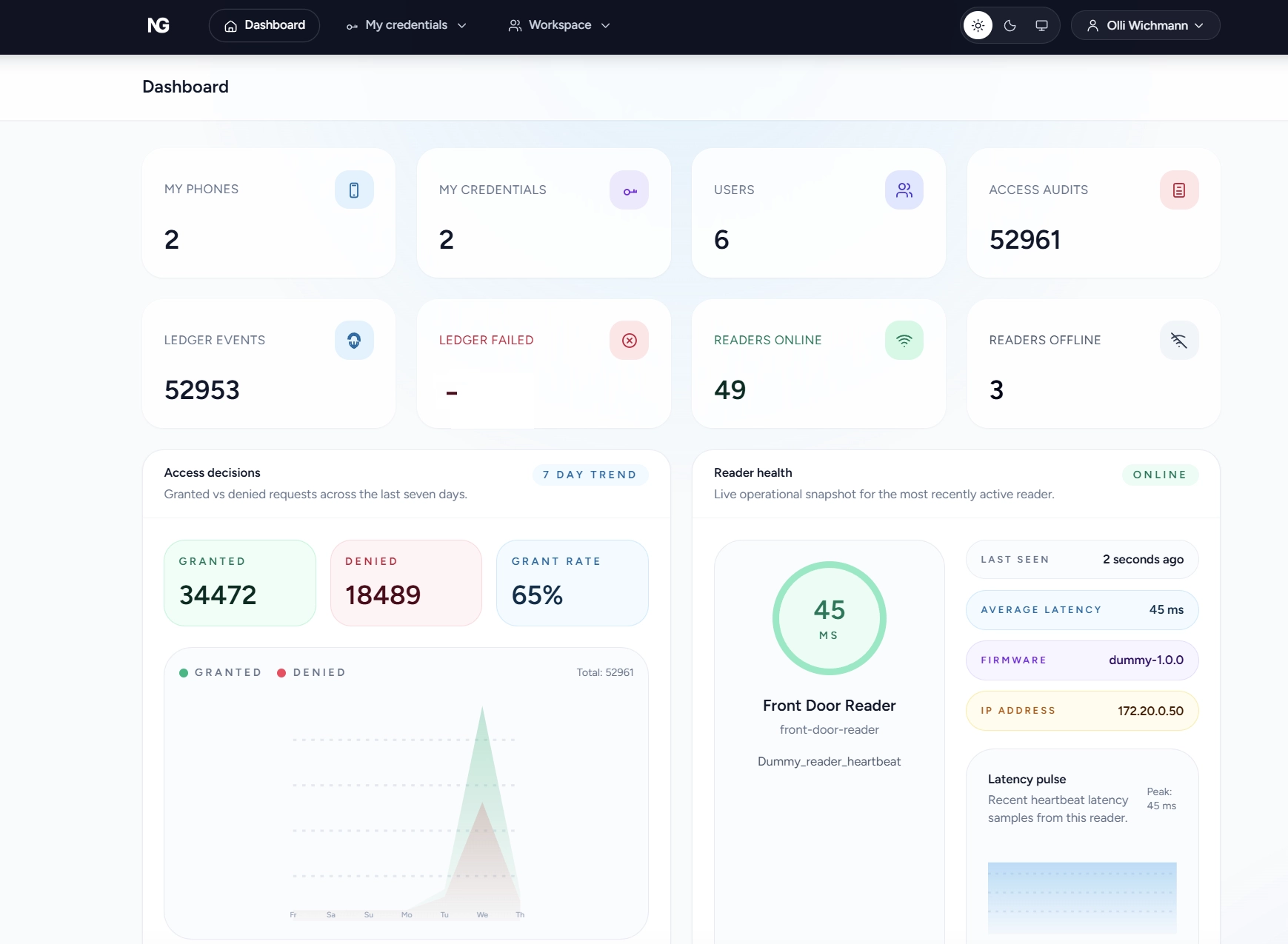
Smart readers, NFC mobile key approval, and effective access stay directly connected to the cloud.
Provision runtime details, claim flows, local permissions, NFC mobile key behavior, and health signals for readers that connect directly to the platform.
Group readers into meaningful operational areas instead of managing every edge by hand.
Apply reusable schedule presets and store the effective permissions on the reader so access decisions keep working offline.
Scan the reader QR code, complete onboarding in under a minute, enable NFC mobile key access, and keep provisioning, commands, and telemetry on a direct cloud path.
Readers support Legic on a Legic 6300 based platform, offer a MIFARE variant, support Matter, Thread, Wi-Fi, BLE, and LAN with PoE, and the hardware can work with Apple Wallet capable scenarios even though NG-Key does not currently provide the Apple Wallet credentials.
See what happened, why it happened, and which ledger event proves it.
NG-Key is built to make access operations inspectable. That includes user activity, reader state, access decisions, effective permissions, ledger events, and blockchain-backed verification paths when verification is enabled.
This turns audit history into something stronger than generic logs: teams can inspect the operational event itself, the related access context, and the associated verification trail in one place. In connected reseller and fulfillment flows, order and handover milestones can also be kept on a traceable commercial event path.
A practical operating stack for controllerless readers, direct cloud delivery, and verifiable access history.
The platform is designed around the components access teams actually operate: a central workspace, Microsoft Entra ID capable identity integration, mobile enrollment, passkeys, smart readers, direct MQTT cloud delivery, reader-resident permissions, scheduled reporting, and audit-grade event history.
That makes NG-Key different from stacks that still depend on separate controllers, higher installation effort, slower commissioning, disconnected audit evidence, and ad hoc stakeholder communication instead of built-in reporting.
A visible security area with whitepapers, operating controls, and deployment discipline.
NG-Key treats security as part of the product and delivery story. That includes platform security foundations, stronger identity posture, credential and reader visibility, protected production delivery, audit traceability, European cloud hosting, GDPR aligned operations, and clear public materials for customers, partners, procurement, and stakeholder review.
Passkeys with FIDO2 and WebAuthn capable flows support stronger authentication posture and cleaner identity assurance.
Administrative ownership, sensitive settings, and invitation hygiene remain visible governance topics.
Deployments can combine public-key credentials with reader hardware for LEGIC and MIFARE-class environments, plus DESFire-linked identifiers where physical media is provisioned.
The cloud footprint is positioned in Europe, aligned with GDPR / DSGVO aware operations, and backed by an ISO 27001 certified data-center environment.
Production rollout follows validated Git and CI/CD workflows with builds, formatting checks, static analysis, tests, immutable runtime images, and controlled runtime secrets.
Built around clarity, controlled access, and operational trust.
Users, groups, areas, readers, and schedules remain visible and reviewable.
Credential lifecycle stays connected to the phone and passkey context that produced it.
Health, provisioning, cloud connectivity, offline state, and access decisions can be inspected without leaving the platform.
Administrative control and sensitive settings stay separate from routine actions.
Operational history stays close to the affected entities and can be linked to ledger events and verification evidence instead of disappearing into generic logs.
The page highlights real product views so capabilities, workflows, and operational context stay easy to understand.
Removing separate controller infrastructure and simplifying reader onboarding reduces installation effort and commissioning cost.

